Developing Story
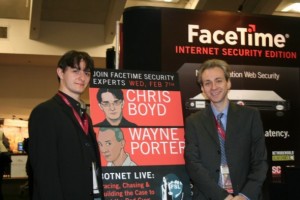
So where are the real threats in the world of adware, malware and spyware? Wayne Porter has been stringing me along for weeks now about the contents of his upcoming coming presentation at RSA. I just got an IM from him, clueing me in on what he and Chris Boyd (PaperGhost to the security world) laid out during their presentation. Hold on to your hats folks, it’s going to be a bumpy ride….
This isn’t  just some install through ActiveX security holes. It isn’t just some buried or long and confusing EULA. It’s not just a cookie being stuffed, an automatic redirect or redirected web traffic. It’s not a gray area of whether the goings on are acceptable or legal. It’s the nasty (and very real) world of botnets, rootkits, Sept 11th ties and criminals. Yes, criminals as in some very not nice people who broke some very real laws.
Wayne and Chris laid out for a packed audience at RSA how they tracked down the parties behind two very sophisticated botnet rings and put the whammy on them. These were case studies to illustrate the current landscape of the world of botnets. We’re not talking some high school kid here getting their rocks off by infecting computer with a trojan or worm through IRC that gets shut down in short order. The two botnet case studies focused on were the Carder (1,2) and Q8 Army Botnets. Do yourself a huge favor…click those links and read. In the case of Carder, which was operating in the US, law enforcement agencies were able to become involved and act. With Q8 Army, while they are still in operation, their activities were dimished. Wayne has promised me more detailed information is on the way and I’ll be updating here as it is released. I’ve already started a list of questions I want to ask him, althogh he doesn’t know it yet. While he’s still traveling and will not be back home for a few days yet, I’m hoping to have him (and maybe Chris) on a podcast talking about the current state of affairs in the world of botnets, malware and adware.










Pingback: Have You Paid A Hacker Today?